Umbra: A Visual Analysis Approach for Defense Construction Against Inference Attacks on Sensitive Information
Xumeng Wang, Chris Bryan, Yiran Li, Rusheng Pan, Yanling Liu, Wei Chen, and Kwan-Liu Ma
IEEE Transactions on Visualization and Computer Graphics, 2020
Abstract
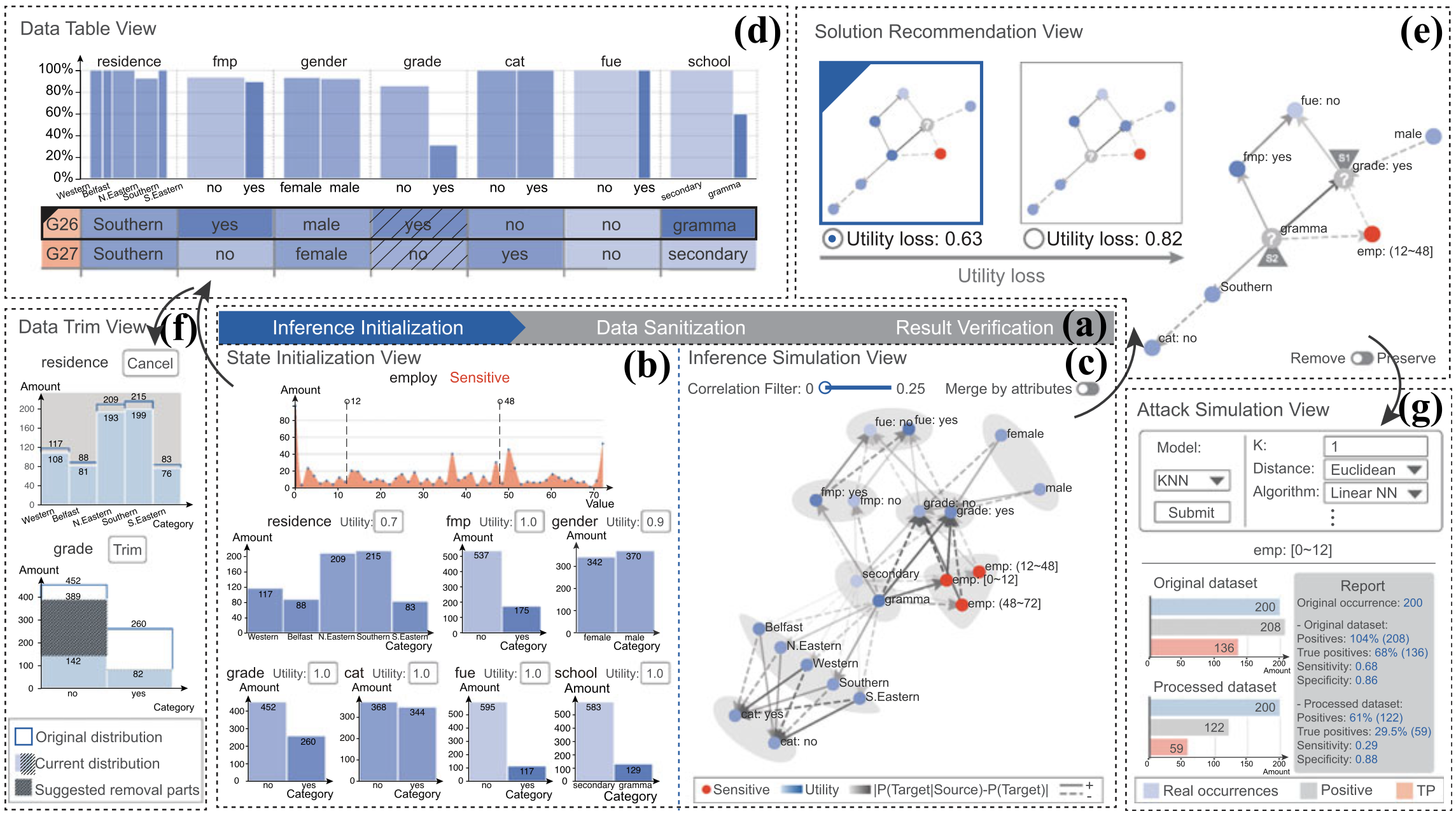
Collecting and analyzing anonymous personal information is required as a part of data analysis processes, such as medical diagnosis and restaurant recommendation. Such data should ostensibly be stored so that specific individual information cannot be disclosed. Unfortunately, inference attacks—integrating background knowledge and intelligent models—hinder classic sanitization techniques like syntactic anonymity and differential privacy from exhaustively protecting sensitive information. As a solution, we introduce a three-stage approach empowered within a visual interface, which depicts underlying inference behaviors via a Bayesian Network and supports a customized defense against inference attacks from unknown adversaries. In particular, our approach visually explains the process details of the underlying privacy preserving models, allowing users to verify if the results sufficiently satisfy the requirements of privacy preservation. We demonstrate the effectiveness of our approach through two case studies and expert reviews.
BibTex
@article{wang2020umbra,
title={Umbra: A visual analysis approach for defense construction against inference attacks on sensitive information},
author={Wang, Xumeng and Bryan, Chris and Li, Yiran and Pan, Rusheng and Liu, Yanling and Chen, Wei and Ma, Kwan-Liu},
journal={IEEE Transactions on Visualization and Computer Graphics},
volume={28},
number={7},
pages={2776--2790},
year={2020},
publisher={IEEE}
}